Hi guys hope that you are having fun solving CTFs.
Yesterday, I posted a writeup on flag 0 of Micro-CMS and so for today we will be continue to solve the remainder flag of Micro-CMS v2.

Flag 1
The given hint is “What actions could you perform as a regular user on the last level, which you can’t now?”.
At first by looking at the hint, I thought the actions was being able to access the pages to edit and published it but I was wrong, and I realized that the actions is referring to user sending HTTP request to the server. (OH I AM SO DUMB 🤪)
I do inspect element on my browser, went to the Network tab and start playing around with the request headers. I first send HTTP request method ‘OPTIONS’ to the server, and I received a response message of the request methods that are allowed for the user.
The request methods allowed for a user are…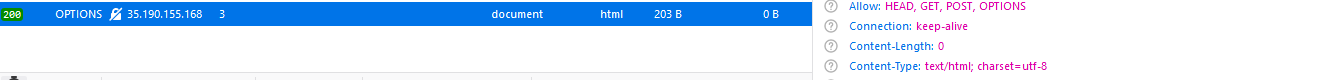
The methods allowed are ‘HEAD’, ‘GET’, ‘POST’
So I get ready my burp suit, turned on the intercept button and starting looking at the different HTTP request method send to the server. HTTP request method such ‘HEAD’ and ‘GET’, I received the response message ‘200 OK’ from the server, however for ‘POST’ method.
I have received the response message ‘400 Bad Request’.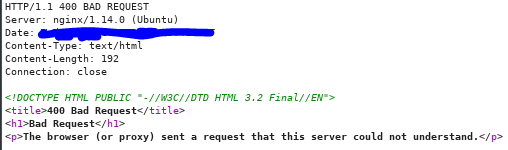
So I was thinking, did I do something wrong with the request like have syntax error etc. However, I checked the request header and there was no malformed request send to the server.
I was frustrated and just couldn’t figured out the reason so I went to get more hints. (I am sorry, I am a noob 😭😭. DON’T JUDGED)
The extra hints given is “Just because request fails with one method doesn’t it will fail with a different method” (This one I literally don’t understand what it mean because I have already tried all the methods and the only methods that fail is ‘POST’). The other hint is “Different requests often have different required authorization”.
What is authorizing me to edit the pages and republishing it, was the session cookie given to the user once he/she has authenticated. So, I removed the session cookie in the request header and send the request header with the ‘POST’ to the server. 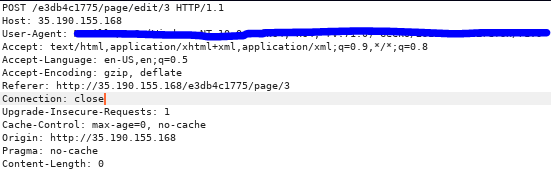
And the response message I get was ‘200 OK’ and the flag as well 🙂
Yah we finally solved flag 1 🙂 Now lets move on to flag 2.
Flag 2
The given hint is “Credentials are secret, flags are secret. Coincidence?”
After scanning through the whole web page, there is no hint of the 3rd flag. Since we did not login as the actual user, thus it might be because of not authenticating as the actual user, we are not able to get the 3rd flag.
Back to the login page, since the web page is vulnerable to SQL injection, we can actual perform blind SQL injection to enumerate the database to retrieve the credentials of an actual user.
There are 2 ways to approach while doing Blind SQLi, either manually or automatically. Of course, we will go with automatically because it is time efficient & I am lazy 🙂 , 
so we are going to need SQLMAP tool. However, I will be posting a blog on doing blind SQLi manually for this CTF, I will put the link below.
Time to enumerate the database using sqlmap command.
sqlmap -u "http://35.190.155.168/8fbc7a0dbf/login" --data "username=&password=" --method POST --regexp "Invalid password" --dumpBeside the options ‘-u’ & ‘–data’, I decided to include the option ‘method’ as data is send via ‘POST’ and the option ‘regexp’ which is regex expression to tell the tool what to look out for if the result return as true.
The result is…
YAHHH, we are able to retrieve the user’s credential from the database and now we will be able to login posing as them. Let’s go back to the login page and input the values.
Note: The sqlmap will also enumerate out the table ‘pages’ where you will be able to see the answer for the flag 0 but I will not dive into that any further.
In the login page,
After login in, we will be able to get the flag ><
And we have come to the end of solving Micro-CMS v2 CTF.
Hope you have a nice day and have fun hacking.
Edit: I have already done Manual Blind SQLi. Click the link here
This one was pretty tough for me, so many many thanks for your report. It helped me a great deal.
LikeLike