Hi guys, hope you have a nice day at work/school 🙂
So now we will be doing more CTF 🏴 !!!!
We will now do version 2 of Micro-CMS CTF, before that if you have not done version 1 of Micro-CMS, I would suggest you to do part 1 of it first. Here is the writeup if you need it.
Lets get our hands dirty and our brain working 🧠
Here is the overview for this CTF:
- Name: Micro-CMS v2
- Difficulty: Moderate
- Total flags: 3
Flag 0
The given hint is “Regular users can only see public pages”.
It is the same as Micro-CMSv1 where users are able to edit/create pages however this time, they require users to be authenticated before editing or publishing any pages.
Since users need to authenticate by submitting an username and password, it can be easily defined that the web application need to retrieve the username and password to ensure that the inputted values are correct before authenticating the user.
How we should approached it? Add a single apostrophe ” ❜ ” in the input box, this is identify whether or not the input box is susceptible to SQL Injection vulnerability. 
The error message will appear….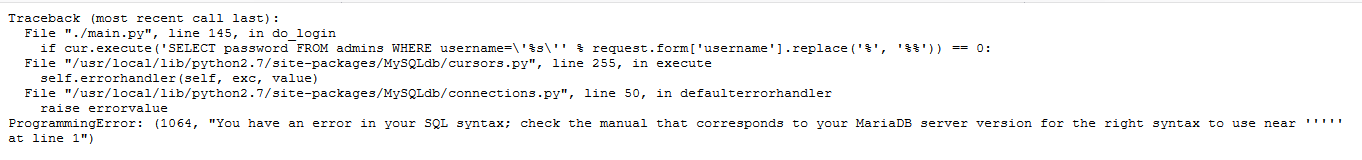

Damm right it is a SQLi vulnerability, as we can identify the SQL statement that is sent to the database to be executed.
SQL statement:
SELECT password FROM admins WHERE username=’ ‘
Let’s try to insert always TRUE statement and input some random password.
The result is…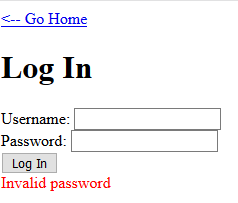
Even if we had input both TRUE statement into both input box, it will still return invalid password as SQL statement retrieve the password and compared it with the inputted value and since the inputted password does not match with any password in the database.
I went to get more hint, the hint given is “Getting admin access might require a more perfect union”
Since Union statement is a must, I was thinking what if we were to set the password where the username is always true, will we be able to bypass the authentication? I did a bit of researched and found out that SQL is able to execute a SELECT statement that include columns containing static string value.
So I was thinking making this SELECT statement
SELECT "qwerty" AS password FROM admins WHERE 1=1I will be able to include these non-existent column with static string value into the returned rows. Another thing to note, is that SQL database do allow 2 columns to have the same name.
Thus, I will be able to input the value “qwerty” for the password and when the SELECT statement is executed, a column “password” will be created filled with static value “qwerty”, where web application will retrieved the value from the column “password” and compared to the inputted value.
Hence, the result will be true, allowing me to bypass the authentication with any username and the password to be “qwerty”.
Here the full SQL injection statement should be…
admin' UNION SELECT "qwerty" AS password FROM admins WHERE '1'='1As columns in each SELECT statement must be in the same order for UNION operator (from w3school, rephrasing it)
resources: https://www.w3schools.com/sql/sql_union.asp
To visualize the whole SQL statement should be…
SELECT password FROM admins WHERE username='admin' UNION SELECT "qwerty" AS password FROM admins WHERE '1'='1LET’S SQL inject it
In the login page, insert the statement and input “qwerty” as the password
Hit the ‘Log In’ button, click the ‘Go Home’ link and you will be able to see three link listed down. 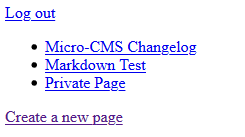
At first glance, you will be able to notice that the private page was not included in the public page. So what would you do?? JUST TAKE A FREAKING LOOK AT THE PAGE !!!(I am not angry)
And there you will be able to find your first flag for this CTF.
That’s all for today, I will be continuing the remainder flag tomorrow.
Have a nice day 🙂
Author: Derek